What is HTB CPTS?
The HTB Certified Penetration Testing Specialist (HTB CPTS) is a highly hands-on certification issued by Hack The Box that assesses intermediate-level penetration testing skills. It covers the full pentest lifecycle — from reconnaissance and exploitation through lateral movement, AD attacks, and commercial-grade report writing.

Unlike multiple-choice certifications, HTB CPTS requires completing a real-world Active Directory pentest against a live network, then submitting a commercial-grade report. There are no shortcuts.
To even sit the exam, you must complete all 28 modules in the Penetration Tester job-role path on HTB Academy — each with its own hands-on skills assessment.
Knowledge domains
The certification evaluates the following areas:
| Domain | Topics |
|---|---|
| Recon & OSINT | Information gathering, footprinting, web recon |
| Web exploitation | SQLi, XSS, LFI, file uploads, command injection |
| Network attacks | Service attacks, password cracking, pivoting |
| Active Directory | Enumeration, Kerberos abuse, AD CS, lateral movement |
| Post-exploitation | Privilege escalation (Linux & Windows), persistence |
| Reporting | Risk communication, commercial-grade pentest reports |
The exam
The exam is a blackbox engagement against a real-world AD network hosted by HTB. You get:
- A letter of engagement with scope and objectives
- Pwnbox or your own VPN connection
- Access to the target network for the exam window
Passing requires both completing the pentest objectives and submitting a full report. No report, no cert — even if you own every box.
Warning (Report matters as much as the flags)
The HTB CPTS exam is explicitly graded on both technical findings and the quality of your written report. A commercial-grade report is a hard requirement, not optional.
My progress
I completed the full Penetration Tester job-role path — all 28 modules including every skills assessment.
I am planning to sit the exam sometime between 2026 and 2027, once I feel the machine track writeups below represent a solid enough review of the core techniques.
Tip (Exam prep strategy)
My current approach: finish the machine track writeups to reinforce AD, web, and privesc chains under time pressure, then move to a full mock engagement before booking the exam.
Machine track
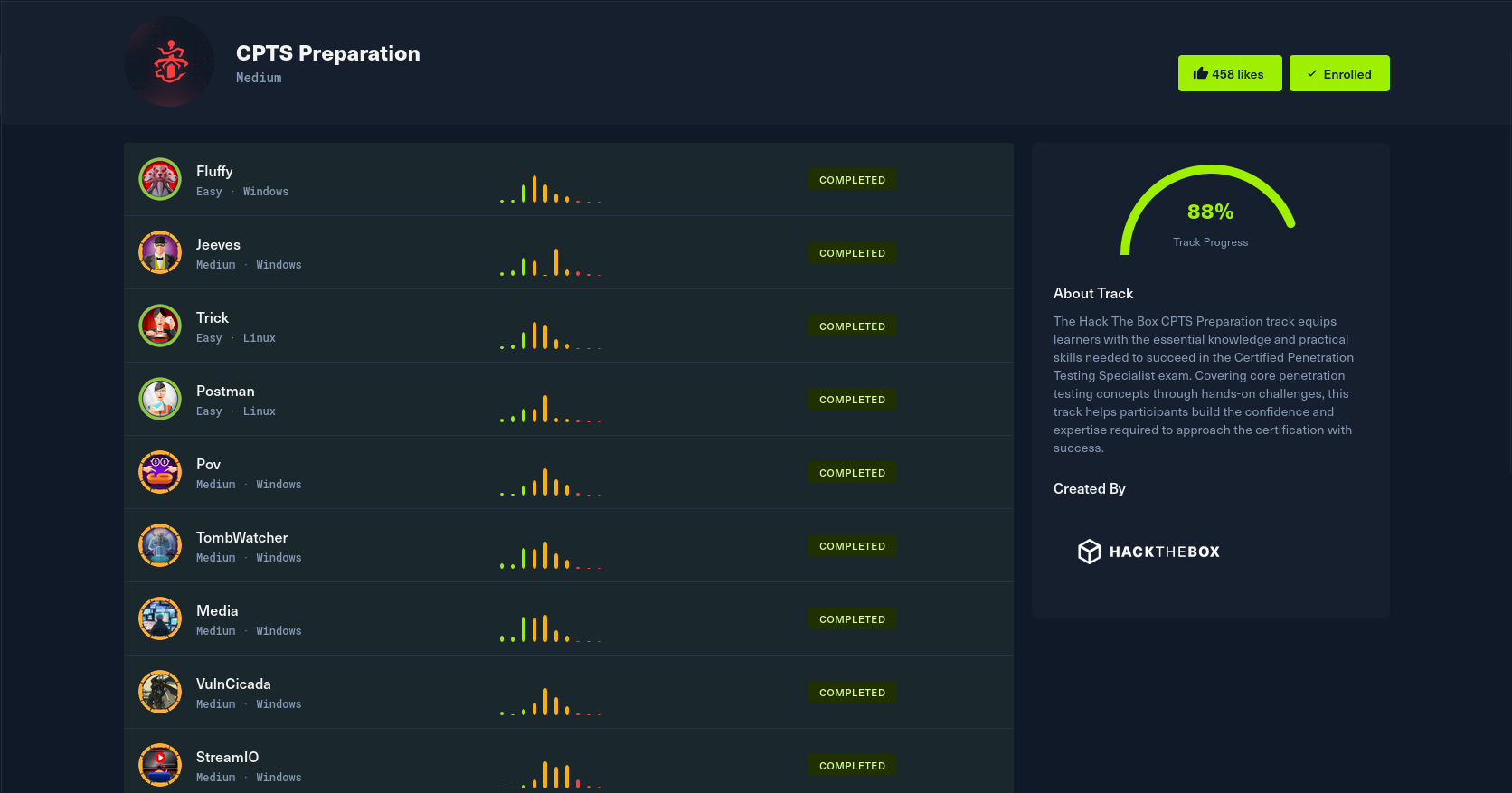
The machines below were selected because they map directly to CPTS learning objectives. Each one is documented as a subpost under this parent entry.
| Machine | OS | Key techniques |
|---|---|---|
| Fluffy | Windows | Assumed breach, ACL abuse, shadow credentials, AD CS (ESC16) |
| Jeeves | Windows | Jenkins RCE, KeePass cracking, Pass-the-Hash |
| Trick | Linux | DNS enumeration, SQL injection, LFI, fail2ban abuse |
| Postman | Linux | Redis abuse, SSH key injection, Webmin RCE (CVE-2019-12840) |
| Pov | Windows | ASP.NET ViewState Deserialization |
| TombWatcher | Windows | |
| Media | Windows | |
| VulnCicada | Windows | AD CS abuse, Kerberos relay (ESC8), DCSync, NFS |
| StreamIO | Windows | |
| Voleur | Windows | |
| Administrator | Windows | |
| Authority | Windows | |
| Craft | Linux | |
| Redelegate | Windows | |
| Snoopy | Linux | |
| Ghost | Windows |
Note (Reading this series)
Use the subposts navigation on this page to jump into a machine writeup directly. On desktop it appears in the right sidebar; on mobile it sits in the sticky header area. New machines will be added here as I progress through the track.
